State cannabis regulators have issued thousands of security-related violations in the past year alone, with penalties ranging from hefty fines to license suspensions. As enforcement tightens and criminal tactics evolve, dispensary owners in 2025 must go beyond basic compliance to implement robust, multi-layered security strategies that protect both profits and permits. In this blog, let’s go through the dispensary security essentials your business needs.
The Current Security Landscape
2025 brings new challenges like:
- Increased cyber threats targeting cannabis businesses
- Stricter state compliance requirements across multiple jurisdictions
- Higher insurance demands for comprehensive security coverage
- Advanced criminal tactics require upgraded countermeasures
- Federal banking scrutiny demands enhanced financial security
The stakes have never been higher:
- Average security breach costs – $250,000-$500,000
- Compliance violations – $10,000-$100,000 in fines
- License suspension risk – 30-90 days for major violations
- Insurance premium increases – 50-200% for non-compliant facilities
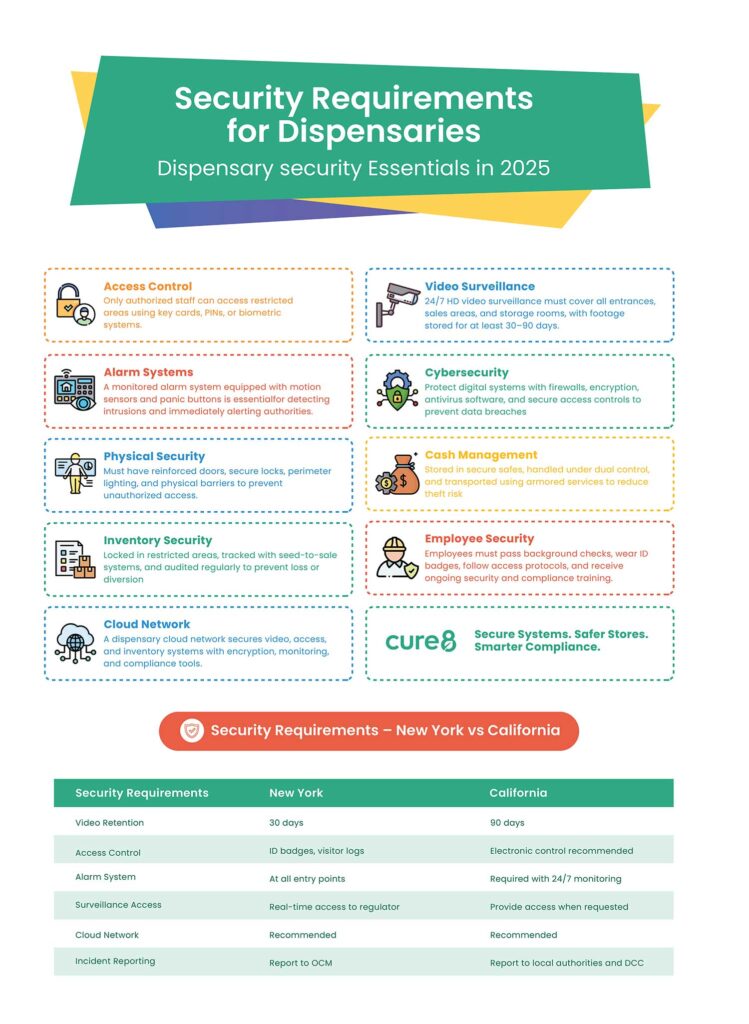
Dispensary Security Essentials in 2025
Video Surveillance – Your Digital Watchdog
2025 Technical Requirements
- 4K resolution minimum for all critical areas
- AI-powered analytics for suspicious behavior detection
- Cloud storage integration with local backup redundancy
- Mobile app access for real-time monitoring
- Facial recognition capabilities for banned individuals
Coverage Areas (Non-Negotiable)
- All customer and employee entrances/exits
- Point-of-sale transactions and cash handling areas
- Product storage, vault, and inventory management zones
- Loading docks and delivery vehicle staging areas
- Perimeter boundaries and parking facilities
Compliance Must-Haves
- Minimum 90-day footage retention (some states require 180 days)
- 24/7 continuous recording with no gaps or blind spots
- Tamper-evident systems with immediate alert capabilities
- Law enforcement access protocols within 24 hours
- Regular system health checks and maintenance logs
Access Control – Who Goes Where, When
Smart Access Solutions for 2025
- Biometric authentication (fingerprint, retinal, facial recognition)
- Multi-factor authentication combining cards, codes, and biometrics
- Time-based access restrictions prevent after-hours entry
- Role-based permissions limit access by job function
- Real-time monitoring with instant alerts for violations
Critical Access Points
- Customer areas – Basic access with visitor management
- Employee work zones – Standard employee credentials required
- Inventory storage – Elevated permissions for authorized staff only
- Cash handling areas – Dual-person access requirements
- Vault/high-security zones – Manager-level approval needed
Alarm Systems – Your 24/7 Guardian
Advanced Detection Technology
- Smart motion sensors with pet immunity and false alarm reduction
- Glass break detectors using acoustic and shock wave analysis
- Environmental monitoring for temperature, humidity, and air quality
- Panic buttons at strategic locations throughout the facility
- Integration capabilities with video and access control systems
Professional Monitoring Services
- 24/7/365 monitoring by licensed security professionals
- Multi-path communication (cellular, internet, landline backup)
- Immediate response protocols with law enforcement coordination
- Real-time mobile alerts to owners and management
- Regular system testing and maintenance schedules
Physical Security – Your First Line of Defense
Structural Hardening
- Commercial-grade locks on all entry points
- Reinforced door frames and high-security hinges
- Security film or bars on accessible windows
- Adequate exterior lighting
- Clear sight lines eliminate hiding spots around the building
Interior Security Measures
- Drop safes for regular cash deposits throughout the day
- Time-delay vault for high-value inventory and cash storage
- Segregated storage areas based on product value and type
- Limited customer access with clearly marked boundaries
- Employee-only zones with restricted access protocols
Perimeter Protection
- Fencing requirements wherever mandated by local regulations
- Landscape maintenance prevents concealment opportunities
- Parking lot security with adequate lighting and surveillance
- Utility access points secured against tampering
- Loading area security with controlled access procedures
Cybersecurity – Protecting Your Digital Assets
Network Security Essentials
- Next-generation firewalls with intrusion detection and prevention
- Encrypted wireless networks using WPA3 security protocols
- Regular security updates and patch management procedures
- VPN access for secure remote management capabilities
- Network segmentation isolates critical systems
Cloud Network Security (Critical for 2025)
- Zero-trust architecture requires verification for every access request
- Multi-cloud security management across different service providers
- Encrypted cloud storage with cannabis-compliant data residency
- Cloud-native security tools integrated with existing infrastructure
- Automated threat detection using AI-powered cloud monitoring
- Secure cloud backup with geo-redundant storage solutions
- Cloud compliance auditing, ensuring regulatory adherence across platforms
- Real-time cloud security monitoring with 24/7 threat response
Hybrid Infrastructure Protection
- Secure cloud-to-premise connectivity with encrypted tunnels
- Consistent security policies across on-premise and cloud environments
- Cloud workload protection for virtualized dispensary systems
- Container security for cloud-based POS and inventory applications
- API security gateways protecting cloud service integrations
Data Protection Measures
- PCI DSS compliance for credit card transaction security
- Customer data encryption both in transit and at rest
- Employee information security with role-based access controls
- Regular security audits and vulnerability assessments
- Incident response planning with clear escalation procedures
- Cloud data loss prevention prevents unauthorized data transfers
- Backup encryption with immutable cloud storage options
Staff Training Requirements
- Phishing awareness and email security best practices
- Password management using enterprise password managers
- Social engineering prevention and verification procedures
- Mobile device security for business-related communications
- Cloud security best practices and safe usage protocols
- Regular refresher training and security awareness updates
Cash Management – Minimizing Your Biggest Risk
Daily Cash Procedures
- Dual custody requirements for all cash handling and counting
- Register limits are typically capped at $500-$1,000 maximum
- End-of-day procedures with manager verification and documentation
- Armored car services for deposits exceeding daily limits
Secure Storage Solutions
- Time-delay safes prevent immediate access to large amounts
- Multiple safe locations distribute risk across the facility
- Limited access personnel with proper authorization levels
- Emergency cash procedures for after-hours situations
- Regular safe maintenance and combination changes
Employee Security – Your Human Firewall
Comprehensive Background Screening
- Criminal history checks at the federal, state, and local levels
- Regular re-screening annually or as required by regulations
- Reference verification from previous employers
- Drug testing compliance with state and local requirements
- Ongoing monitoring for new criminal activity
Security Training Programs
- Emergency response procedures for various threat scenarios
- Customer interaction protocols, including de-escalation techniques
- Cash handling security and theft prevention measures
- Incident reporting procedures with a clear chain of command
- Regular training updates as regulations and threats evolve
Regulatory Compliance – Staying Current
State-Specific Requirements
- Regular compliance audits and documentation reviews
- Reporting procedures for incidents and security breaches
- Documentation retention for 3-7 years, depending on jurisdiction
- Law enforcement cooperation protocols and response procedures
- Policy updates reflecting current regulatory changes
Emergency Preparedness – When Things Go Wrong
Incident Response Planning
- Robbery response protocols prioritizing employee and customer safety
- Medical emergency procedures with first aid and Automated External Defibrillator (AED) training
- Natural disaster preparedness, including evacuation procedures
- Cybersecurity incident response with IT and legal team coordination
- Business continuity planning for operational recovery
The Bottom Line – Invest in Security Today
Security is not just compliance – it’s smart business
- Increased customer confidence in your professional operations
- Protection of valuable assets, including inventory, cash, and data
- Peace of mind for owners, employees, and customers
- Competitive advantage in an increasingly regulated industry
Partner with Security Experts
Navigating the complex world of dispensary security requires expertise and experience. Working with security professionals who understand the cannabis industry ensures you’re not just meeting minimum requirements – you’re implementing best practices that protect your business, employees, and customers while maintaining full regulatory compliance.
Your security investment today determines your business success tomorrow. Don’t wait for an incident to realize the importance of comprehensive protection.